The IT to OT transition into a substation environment is not a credential problem — it is a sequencing problem. Engineers who come from IT backgrounds with strong networking, firewall, and protocol skills often have most of the technical building blocks already. What they are missing is the specific substation context: how protection systems work, why availability is non-negotiable, what IEC 61850 is actually for, and how the physical environment (a live 400kV switchyard) shapes every engineering decision made in the design office.
What the IT-to-OT Transition in a Substation Actually Requires
The knowledge gap between IT and substation OT is not primarily about certifications. It is about understanding the operational constraints of a power system. A few that regularly trip up IT engineers making the transition:
Availability first, always. In IT, patching a server that takes it offline for 30 minutes is a routine maintenance event. In a substation, taking a protection IED out of service requires a formal outage plan, coordination with the control centre, backup protection being verified as available, and a return-to-service test. The process exists because the consequence of an unprotected bay is a bus fault with no trip.
Protocols have physical consequences. Misconfiguring a GOOSE subscription does not produce an error log — the IED simply does not receive the signal. If that signal was an inter-trip command, the first indication that it was absent is a protection failure during a fault. This is different from misconfiguring a firewall rule that generates an alert.
The network is the protection system. As covered in the network design article — substation LAN design is a protection engineering discipline. An IT engineer accustomed to adding a switch to a network needs to understand that adding an unqualified switch to a GOOSE path can degrade protection performance.
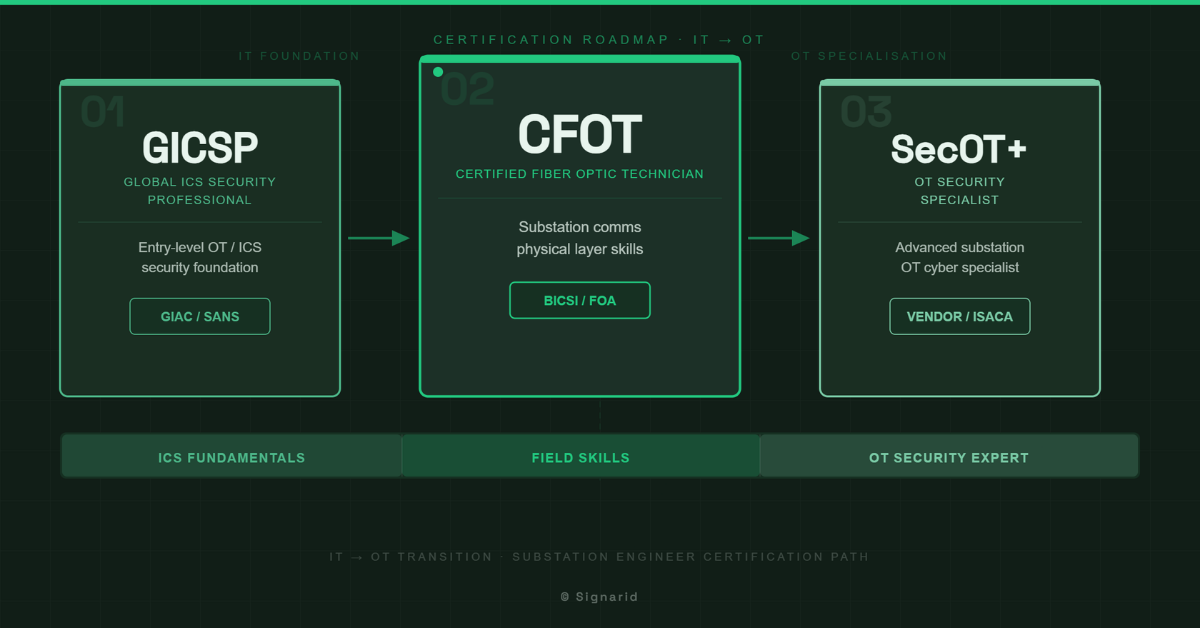
The Certification Sequence That Makes Sense
For an IT engineer transitioning into substation OT, the certification sequence that provides the most structured ramp:
Step 1 — GICSP (Global Industrial Cyber Security Professional) — GIAC/ICS-CERT. This is the entry credential for ICS/OT cybersecurity. It covers the Purdue Model, ICS protocols, SCADA architecture, and security controls in an industrial context. For someone with an IT security background, much of the material is familiar — but the ICS-specific sections (PLC, SCADA, historian, HMI security) provide the OT framing that IT certifications do not. This is the right starting point because it gives you the vocabulary and the architectural model.
Step 2 — CFOT (Certified Fibre Optic Technician) — FOA. This may seem like a step down from a cybersecurity credential, but for anyone who will be working in or around substation commissioning, fibre optic fundamentals are practical knowledge. Substation LAN runs on fibre. SFP selection, connector types, testing with an OTDR, understanding loss budgets — these come up at FAT and on site. The CFOT is a fast credential (a few days of study for someone already technically proficient) that removes a common gap.
Step 3 — SecOT+ or equivalent OT security practitioner credential — This layer builds on GICSP with more depth in operational security practice: patch management in OT environments, network segmentation implementation, incident response in an ICS context. The specific credential depends on what the target employer or utility recognises — in GCC and India, GICSP tends to be the benchmark, but SecOT+ adds credibility for roles specifically in the security architecture space.
What Certifications Do Not Replace
Certifications validate that you understand the concepts. They do not replace the operational experience of having configured an IED, traced a GOOSE fault, or understood why a protection scheme was designed the way it was. The engineers who make the IT-to-OT transition most effectively are the ones who pair the certification path with structured technical training that covers real commissioning scenarios — not just compliance frameworks.
The sequencing matters because the wrong order wastes time. Attempting GICSP without any ICS/substation context leads to heavy memorisation of terms without intuition. Building the substation fundamentals first — IEC 61850 architecture, protection principles, OT network design — and then acquiring the GICSP gives the certification exam a framework to hang on.
Internal links: For the OT cybersecurity foundation that supports this transition, see [Substation OT Cybersecurity]. For the protocol knowledge an OT engineer needs, see [GOOSE Protocol in the Substation].
Signarid’s training is designed specifically for the IT-to-OT transition — structured around real substation projects, covering the technical gaps that certifications do not fill. Enquire about a training programme.