Substation OT cybersecurity is a discipline that borrows the language of IT security — firewalls, VLANs, RBAC, audit logs — but applies them in an environment where the consequences of a misstep are measured in megawatts, not data breaches. Understanding where security controls belong in a live switchyard, and why the IT security instinct can be the wrong one here, is the starting point for any engineer working in this space.
Why Substation OT Cybersecurity Is a Different Problem
In IT, the security priority order is confidentiality → integrity → availability (CIA). A data breach is the worst outcome. In a substation, that order is reversed: availability → integrity → confidentiality (AIC). If a protection relay trips a 400kV busbar, availability is the first thing that matters. The grid cannot wait for a renegotiated TLS session.
This distinction shapes every security decision in the substation. A firewall rule that blocks an unexpected MMS port during a live event is not protecting the substation — it is creating one. Deep packet inspection on a GOOSE message path adds latency that can compromise protection performance. These are not hypothetical failure modes.
The Purdue Model in a Substation Context
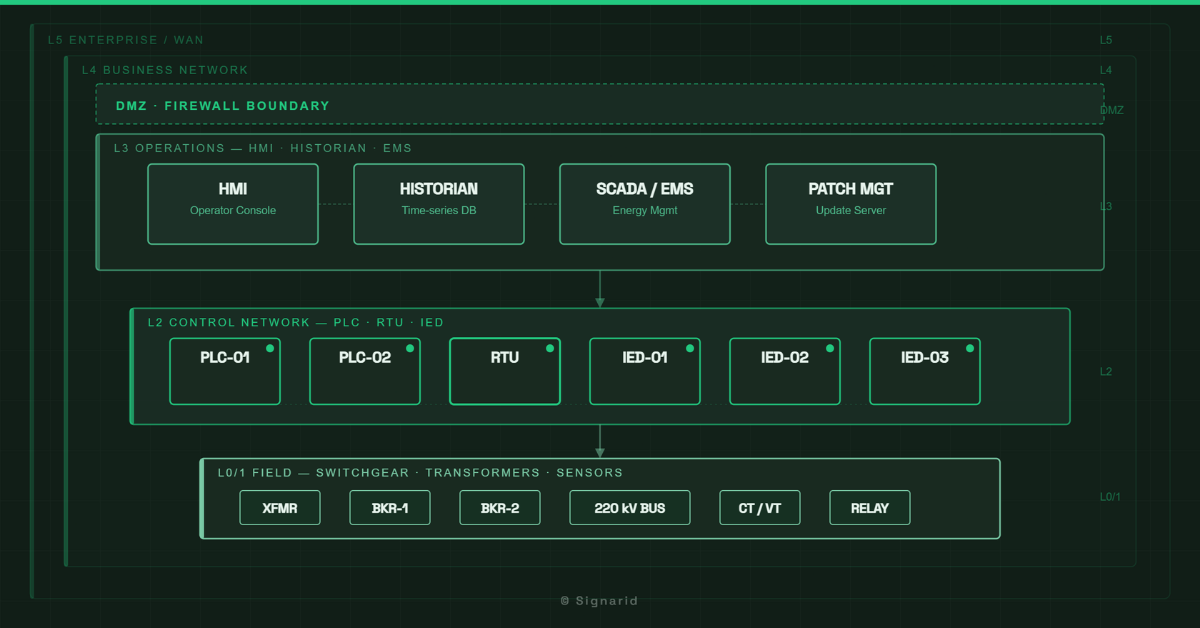
The Purdue Model, adapted for ICS/OT, gives a useful starting framework. In a substation context:
- Level 0 — Field devices: CTs, VTs, circuit breakers, primary equipment
- Level 1 — IEDs: protection relays, merging units, bay controllers
- Level 2 — Station level: HMI, historian, engineering workstation, gateway
- Level 3 — Operations: SCADA, EMS, control centre
The security boundary that matters most is between Level 2 and Level 3 — the substation gateway to the SCADA network. This is where a properly configured industrial firewall belongs: stateful inspection on IEC 60870-5-104 or DNP3 sessions, strict VLAN separation, no direct routable path from the corporate network into Level 1 or Level 2.
The most common mistake: placing a generic IT firewall at the substation boundary and applying enterprise security policies to Level 1 IED traffic. GOOSE and Sampled Values are multicast — they do not have the kind of session state that a stateful firewall understands cleanly.
Where NERC CIP and IEC 62351 Apply
NERC CIP (Critical Infrastructure Protection) standards apply primarily to bulk electric system assets in North America, but utilities in GCC and India increasingly reference them as a design benchmark — particularly for substations integrated into national grid control centres. The standards most relevant at substation level are CIP-005 (Electronic Security Perimeters), CIP-007 (Systems Security Management), and CIP-010 (Configuration Change Management).
IEC 62351 is the security standards family developed by Working Group 15 (WG15) of IEC Technical Committee 57 (TC 57). It was developed specifically to address security across the entire TC 57 series of power system communication protocols — not just IEC 61850. The scope covers:
- IEC 60870-5 series — telecontrol protocols including IEC 60870-5-101 (serial) and IEC 60870-5-104 (TCP/IP)
- IEC 60870-6 series — inter-control centre communications (ICCP/TASE.2)
- IEC 61850 series — substation automation, GOOSE, MMS, Sampled Values
- IEC 61970 series — Common Information Model (CIM) for energy management systems
- IEC 61968 series — CIM for distribution management systems
This is an important distinction: IEC 62351 is not a bolt-on security layer for IEC 61850 alone. It is the unified security framework for the entire TC 57 protocol ecosystem. Engineers working across SCADA, EMS, and substation automation layers will encounter it at every boundary.
The parts most directly relevant at substation level:
- IEC 62351-3: TLS for TCP/IP-based protocols (including MMS over TCP and IEC 60870-5-104)
- IEC 62351-6: Security for IEC 61850 — authentication for GOOSE and Sampled Values
- IEC 62351-7: Network and system management data object models
- IEC 62351-8: Role-based access control (RBAC) for power system devices
IEC 62351 is the right reference for protocol and IED-level security across the full TC 57 stack. NERC CIP is the right reference for programme-level compliance. Both are needed — they operate at different layers. A dedicated article on IEC 62351 across the TC 57 family is planned as a Phase 2 cluster post under this pillar.
Jump Hosts, RBAC, and Audit Readiness
Three controls that make a measurable difference at audit time:
Jump hosts (bastion hosts): All remote access to the station LAN should route through a hardened jump host in the DMZ. No direct VPN tunnel to Level 1 or Level 2. The jump host logs every session, every command. This is the single most cited finding in substation security audits — direct remote access without a jump host.
RBAC: Role-based access control on IEDs limits who can read, configure, or control. Most modern IEDs support RBAC at the firmware level. It is rarely configured correctly at commissioning because it comes late in the project timeline. The result is that engineer-level access is left on every device indefinitely.
Audit logs: Historians and HMI systems should capture configuration changes and access events with timestamps. This is a NERC CIP CIP-007 requirement and a practical necessity for any post-incident forensics.
Internal links: For the network design layer that supports these security zones, see [Designing Substation Networks for Sub-4ms Protection]. For IEC 61850 architecture context, see [Station Bus vs. Process Bus].
Signarid’s corporate training covers OT cybersecurity from the substation floor up — including NERC CIP readiness, IEC 62351 implementation, and the RBAC and jump host configurations that auditors look for. Enquire about a training programme.